What Happens When the Plug Gets Pulled?
What Happens When the Plug Gets Pulled?
“America is the greatest superpower this world has ever known,” wrote Trumpet editor in chief Gerald Flurry in 1995. “But we have a very vulnerable point in our military—our own Achilles heel. It is so dangerous that I am amazed it hasn’t received more publicity.”
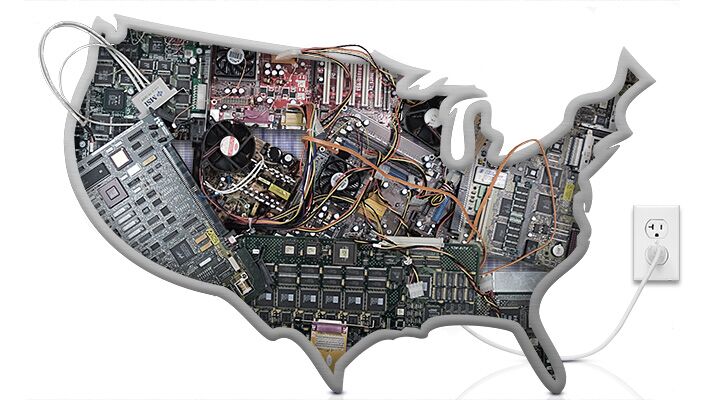
The deadly weakness? Cyberwarfare. Twenty years later, it would be easy to assume this problem has been fixed. After all, we’ve known about this vulnerability for decades. America has even set up a United States Cyber Command—a cyberwarfare headquarters. No massive hacking attack has shut down our infrastructure or military. Surely the United States is adequately protected by now?
Sadly, that could not be further from the truth. The average American would be shocked to find out just how much of his daily life is vulnerable to cyberattack.
Cyberwarfare is, by nature, incredibly hard to defend against. But the vast scale of America’s vulnerability reveals a complacency at the heart of America’s defense establishment. Since 1995, this danger has increased dramatically.
Civilian Infrastructure at Risk
Cyberwarfare refers to attacks on a country’s electronic information systems. These systems are connected to real-world operations: military bases, power plants, dams, reservoirs, reactors, energy grids, logistics centers, airports, financial institutions and telecommunications centers. If hackers can gain access to these systems, they may be able to rob, cripple or destroy important information and infrastructure. It is not just military targets that are in danger. Just as in wartime, some of the biggest targets are civilian.
On December 21, the Associated Press published an in-depth study on the vulnerability of the U.S. electric grid system to cyberattacks. It said, “About a dozen times in the last decade, sophisticated foreign hackers have gained enough remote access to control the operations networks that keep the lights on, according to top experts who spoke only on condition of anonymity due to the sensitive nature of the subject matter.”
“The public almost never learns the details about these types of attacks,” the report said, adding that many attacks “are never even reported to the government. These intrusions have not caused the kind of cascading blackouts that are feared by the intelligence community. But so many attackers have stowed away in the largely investor-owned systems that run the U.S. electric grid that experts say they likely have the capability to strike at will.”
The report warned that much of the equipment used in the grid is “decrepit” and vulnerable to attack. Equipment that was never designed to be connected to the Internet is now online—and vulnerable. To make matters worse, the age of the infrastructure could mean that damage caused by an attack could take months to fix.
In a cyberattack on the energy company Calpine, which manages power stations across the United States, hackers gained access to usernames and passwords, enabling them to connect remotely to the network. The intruders accessed detailed engineering drawings of Calpine networks and power stations and information on how each power plant communicates with the others. This is enough information to shut down generating stations and cause blackouts and enough technical information to gain control of a network while still being able to hide an attack.
Iran has been identified as the most likely culprit for this attack. These same hackers also accessed the systems of Pakistan International Airlines, Mexican oil giant Pemex, the Israel Institute of Technology, and the Navy Marine Corps Intranet.
An attack on an electrical grid was only theoretical—until 2015. On December 23, a computer program gave hackers access to the systems of Prykarpattya Oblenergo, a Ukrainian electricity provider. They shut down the power to 80,000 homes for six hours, and kept the company from discovering the attack by flooding it with phone calls so customers could not report the outage.
All this exposes the vulnerability of just one target: the U.S. power grid. Other industries have also been hit. In 2014, hackers infiltrated a steel mill in Germany and prevented its blast furnace from being safely shut down, causing what Germany’s Federal Office for Information Security described as “massive damage.” More recently, Iran hacked the control infrastructure of a dam in New York. The details of this attack are classified.
“Unfortunately, many accounts of cyberattacks these days seem to produce yawns,” the Washington Post wrote Aug. 12, 2015. America has been vulnerable to cyberattacks for so long that now it’s just old news.
After giving a litany of examples of cyberattacks, the Post wrote, “[Y]et the United States has been complacent and lazy in responding.”
“Doing nothing is not an acceptable option,” the Post wrote. But that’s all the U.S. is doing.
History’s Costliest Weapon System
So far we’ve discussed only civilian assets. But America’s military is also hugely vulnerable. Perhaps nothing symbolizes this vulnerability better than the F-35.
The U.S. Air Force has bet its future on the F-35. With a total projected cost of around $1.3 trillion, the fighter jet is the most expensive weapons system in history. The United States military plans to buy around 2,500 of these planes. In fact, it plans to own more F-35s than all other manned aircraft put together.
This plane is high-tech. It is stealthy. Its pilots wear virtual reality helmets (costing $400,000 each) that allow them to see through walls of the aircraft. If the pilot looks down, for example, images of the ground below appear on his helmet’s visor from infrared cameras mounted on the outside of the airplane.
These capabilities require a powerful computer in the plane. Its designers went all out on computer control—the software is far more complicated than any other fighter ever built. All the instructions the pilot gives to the plane—ascend, bank left, etc.—pass through this computer. The computer controls all the weapons systems. The computer detects when a part is failing or is due to be replaced, orders a replacement and tells the ground crew where to fit it.
That’s the theory. In practice, all these IT systems have been a nightmare. The U.S. has already rolled out approximately 100 F-35s. But its main cannon cannot fire. The cannon is there, but the software to run it is not finished.

But most disturbing is its huge vulnerability to cyberattack. In November 2015, the U.S. canceled its cybersecurity tests on the F-35.
Why? There would have been plenty of bad reasons: complacency, or an unwillingness to spend the extra cash, for example. But these tests were canceled for the worst imaginable reason. Military officials canceled the test because they worried that even a simulated cyberattack could ground all the F-35s currently in operation.
That’s right: The next generation of America’s Air Force is so fragile that just testing its cybersecurity could ground the entire fleet.
Perhaps any plane as computer dependent as the F-35 is going to be vulnerable. But the specific weakness due to be tested last November was completely avoidable. It was the maintenance software—the system designed to automatically order spare parts—called the Autonomic Logistics Information Systems (alis) program. Defense analyst Dan Grazier wrote for the Straus Military Reform Project, at the Project on Government Oversight, that many consider the alis program “the plane’s largest vulnerability.”
“Should an enemy hack the alis system successfully, they could disable F-35 systems in combat, cause disastrous crashes, or ground the entire fleet,” he wrote.
“It’s not as if this is a theoretical threat,” wrote Grazier. “The Department of Defense admitted in 2013 that a foreign power had hacked into unclassified F-35 subcontractor systems and stolen large amounts of sensitive information about the aircraft.”
If defense planners were at all worried about cyberwarfare when commissioning these planes, there would have been a very simple solution: Don’t create a network that links all F-35s together simply to make it easier to order spare parts.
A High-Tech Ticking Time Bomb
Counterfeit electrical parts are another area where a huge range of American military hardware is at risk, and the government has done little to fix the problem.
The U.S. is not at all picky about whom it buys computer parts from. A foreign country wouldn’t need to hack into American computers—it could have all the software it needs built into a computer chip already installed.
Experts have been talking about this problem since the mid-1990s, but nothing has been done.
In 2011, the U.S. nearly installed faulty transistors on a U.S. helicopter that would have prevented the helicopter from being able to fire its weapons. They traced the transistors back through five companies to China. In this case, it was concluded that the flaws were a mistake. But it shows the danger in America’s high-tech weapons systems being dependent on tiny parts from foreign nations. The fear is that a foreign government could easily do the same thing with deliberately designed fake parts. One may have even done so already.
“Microchips are the bedrock upon which our digital world is based, and they are almost entirely unsecured,” Popular Science wrote Feb. 17, 2015.
One of the reasons these types of problems haven’t been addressed is that they are so hard to fix. “The potential avenues of attack are so numerous and insidious, they can be hard to contemplate,” Popular Science continued. Cyberattacks using microchips can “hit anywhere hardware exists, from coffeemakers to fighter jets,” it wrote.
Retired Air Force four-star Gen. Michael Hayden, who headed both the Central Intelligence Agency and National Security Agency, was asked about hardware hacking in 2011. “It’s the problem from hell,” he stated.
“Frankly, it’s not a problem that can be solved,” he said. “This is a condition that you have to manage.”
A huge number of the electrical parts in the F-35 come from China. Any one of a number of these chips could disable the whole system. Counterfeit chips could be programmed to kill the system after receiving a specific signal, or after a predetermined amount of time, for example. But with billions of transistors in a single system, it’s impossible to even check most of them.
The U.S. has some programs in their infancy to help stop this problem. But they are likely too little too late when it comes to securing planes with supercomputers and complex, high-tech parts.
Cyber Spying
Further proof of America’s weakness in this area comes from the related field of cyber espionage. The lines between cyber espionage and cyberwarfare can become a little blurred, but in general, cyber espionage involves spying—stealing data, rather than destroying it.
America’s ability to prevent cyber theft gives us a good indication of how good it would be at stopping cyberwarfare.
Once again, America’s track record is abysmal. Last year, the government suffered its biggest attack in history when the Office of Personnel Management was hacked. A foreign power accessed a trove of sensitive information about 21 million Americans—everything they need to know to figure out who can be bribed or blackmailed, and how to do it.
The Internal Revenue Service was also hacked, and data from 330,000 accounts was stolen. In another incident, even cia Director John Brennan had his personal e-mail account hacked. In this instance the perpetrators appeared to be bored teens. Imagine what a foreign government would be—or is—capable of doing.
Civilian targets have also been hit. Last year, for example, hackers compromised 100 million health insurance records.
The nature of cybersecurity makes it very hard for America to secure itself. As the Washington Post wrote, cyberwar is “asymmetrical, favoring a smaller, stealthy attacker over the defender. The concept of deterrence from the nuclear age—the idea of two cocked pistols preventing either side from shooting—offers limited comfort in a conflict in which attackers often can avoid identification until long after an attack” (op. cit.).
America, with its Cyber Command, is able to carry out cyberattacks—such as the Stuxnet attack on Iran. But to attack, you need to compromise just one system. To defend, you have to stop your enemy from compromising thousands.
A Nation Asleep
The U.S. military has been incredibly complacent. It has barely tried to take effective measures at defense. Civilian planners have been even worse.
This points to a deeper sickness. America’s leaders, military planners and citizens are acting on the assumption they will never have to fight a war with another major power. The whole defense doctrine is geared around fighting a terrorist network, or maybe an Iran or North Korea. If you only expect to be fighting Third or maybe Second World countries, cybersecurity is a nuisance, but not a life-threatening danger.
Many believe that even if China, for example, has completely infiltrated the American electrical grid, it would never shut it down, simply because it would have too much to lose. That is a comforting worldview. It also reflects the way people thought before World War i and at several other times in the past. It’s also a view completely demolished once someone gains even a modicum of historical perspective. Human beings have always fought wars, and human beings have always used the tools of warfare at their disposal.
But this complacency means America’s leaders are asleep to this huge danger.
When Mr. Flurry first wrote on this subject back in 1995, he quoted defense analyst Joseph de Courcy, who wrote, “Computer dependence is the Western world’s Achilles Heel, and within a few years this weakness could be tested to the full.”
Mr. Flurry wrote that de Courcy’s warning immediately reminded him of Ezekiel 7:14: “They have blown the trumpet, even to make all ready; but none goeth to the battle: for my wrath is upon all the multitude thereof.”
“It seems everybody is expecting our people to go into battle, but the greatest tragedy imaginable occurs!” Mr. Flurry wrote. “Nobody goes to battle—even though the trumpet is blown! Will it be because of a computer terrorist?” (January 1995).
Last year, top defense journalists P. W. Singer and August Cole decided to write a novel about what America’s next war could look like. With hundreds of footnotes, their book Ghost Fleet “can come across as a 400-page warning,” as the tech magazine Wired wrote.
In the book, China launches a surprise attack on the U.S. The first shot of this war is against an American satellite (a subject we addressed in our February 2016 issue: “Space: The Final Military Frontier.”) At the same time, the Chinese launch a massive cyberattack. With the U.S. now completely blind, China launches carrier-killer missiles and destroys America’s Pacific Fleet.
As the combined Russian-Chinese attack rolls out—using troop carriers disguised as container ships, for example, something Russia is already working on—it comes up against the F-35. In the authors’ imagination, counterfeit chips inside the F-35 emit a signal that Chinese missiles can home in on. They are easily shot down.
By the time the U.S. Joint Chiefs of Staff knows what is going on, the attack is already over. America has lost: The Pacific Fleet is gone, and Hawaii has been taken.
When some of America’s top military thinkers imagine what America’s next war could be like, they come up with something remarkably like what is recorded in Ezekiel 7, and about which Mr. Flurry warned decades ago.
