Target: America

Target: America
Power’s out. You flick the switch repetitively, still nothing. Your little clock radio is blank; you glance at your cell phone to check the time as you go to the closet. Hopefully you won’t be late for work … “No Signal.” You grab your robe and head down the hall, walking a little quicker now. Daylight is breaking, but the house is dark, the appliances dead.
The muffled sound of your neighbor’s backup generator makes its way into the foyer, so you walk over to see what the news is. Eight network channels, all static—except for two that appear to be airing reruns. Your neighbor looks worried.
You remember your car’s on empty. Whatever is going on, it couldn’t hurt to fill up your tank before people panic and start rushing the gas station. You walk back across the dewy yard, lift the garage door and drive to town, still in your pajamas and robe, wet grass clippings clinging to your feet.
Ten minutes later, you’re in a gridlock parking lot in the middle of the street—still a block and a half from the pumps. It turns out you aren’t the only one who’s worried about gasoline. You flick on the radio, now anxious to know what’s going on. More static. Finally: “Parts of the Eastern Interconnection power grid are failing this morning …. Servers for several news organizations appear to have been abruptly knocked off-line …. Rail, port and air traffic control network computer systems are experiencing glitches …. Numerous banks have temporarily suspended their electronic operations …. Reports are coming in that the Pentagon may have suffered a large cyberattack; some systems have been compromised, others are shut down to contain security breaches ….”
How the rest of this day ends is up to your imagination.
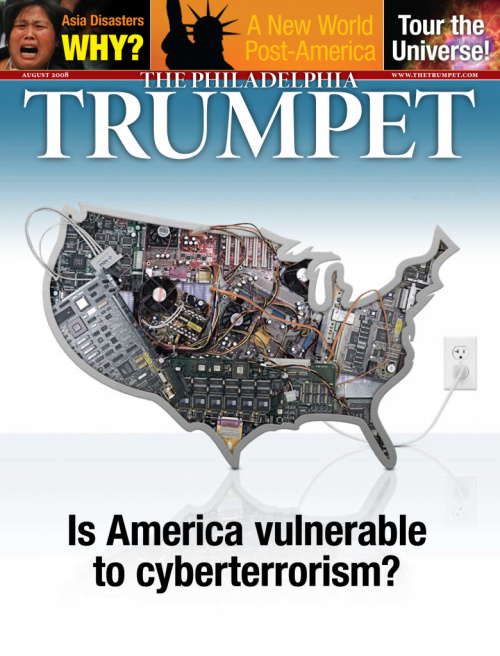
Hidden Danger equals: Digital Underground
The birthplace of the Internet, the United States, is one of the world’s most well-connected nations. Millions of Americans and other Westerners in households, businesses and government agencies use the Web to communicate, do business, transact, administrate day-to-day operations, control infrastructure, monitor world news, research, learn, navigate, shop and socialize. Even infrastructure and government functions, including the United States military, rely on the network. Time- and money-saving network solutions define your world. That’s the good news. And the bad news.
Beneath the everyday hum of businessmen, students, bankers, typists, graphic designers, web programmers, network administrators and other Internet dependents that you can see lies a digital underground that you can’t. In the same way the real world has an illicit and unseen criminal underground, human nature plays out the same way online. Below the global online community’s slick and shiny interface is a world of code—the gears inside the clock. To you, it would look like gibberish, but programmers can read and write it. So can hackers.
Although some use their expertise for benign or even constructive purposes, generally speaking hackers are programmers who use their knowledge of coding and programming to engage in illicit activities ranging from simply viewing sensitive material and playing practical jokes to blackmail, theft and sabotage. In some cases, hackers have brought down business websites, and security programmers have been helpless to restore service. The sites only went back online when the businesses paid their attackers to stop.
Software makers and online security companies are constantly reacting to these threats with “patches” that cover up one vulnerability while hackers move on to find others.
Right now, hackers around the world are writing programs that are searching for unprotected areas of code, finding them and silently slipping past security. Then, they use their imaginations: recording the keystrokes of unsuspecting users, crashing programs, overloading websites, ripping off passwords, stealing account numbers—constantly, silently, anonymously. And their reach increases every time a new computer plugs in.
If you buy a computer this evening, bring it home and plug a network cable into it, chances are it will be compromised within five minutes. You won’t know it, but automated hacker programs will already have found your computer and begun diverting some of your processing power and using your computer’s identity to mask their own activities, which include sending unwanted e-mail advertisements, overloading targeted servers and taking over yet more computers. Constantly updating your antivirus software will help keep incursions to a minimum, but there are no guarantees. In fact, some initial network security downloads take longer to install than it takes for a hacker’s program to penetrate your system.
Generally, hackers aren’t necessarily able to read your e-mail or steal your files. That typically occurs only if someone targets you directly. But when that happens, usually to a larger organization, hackers can be in and out with the information they want and without leaving a trace in under 20 minutes. Or they can disrupt, falsify or outright destroy it.
The New Battlefield equals: Cyberwar
That’s cybercrime, instigated by a largely unorganized group of hackers with varying skills and motivations. But what about all-out cyberwarfare? The potential effects are much more catastrophic. This Internet underworld is the 21st century’s newest battleground.
China, Russia, even Islamist terrorists are beginning to wage a new kind of war here, in an environment where a desktop computer can put your agenda on a level playing field with the world’s only superpower. It’s a cheap, powerful equalizer. And when it comes to the havoc a cyberassault could bring, especially when coupled with a real-world attack, there’s nothing virtual about it.
Case study: What happens when you combine a well-connected, Internet-dependent nation, a hostile enemy, hacker mercenaries and an unpopular political decision? You get Estonia. Surprisingly well-connected, Estonians use the Web heavily in everyday life: for their banking transactions (almost all of them), communications, news, shopping, reservations, theater tickets and more. There, Internet access is legally considered a human right; even parliamentary votes are conducted online.
In April 2007, the government relocated a Soviet-era statue, infuriating ethnic Russians inside and outside of Estonia, as well as the Kremlin.
Within 24 hours, hackers began probing Estonia’s online defenses to test their limits. Then, they blasted key computer targets with information overloads. Parliament’s e-mail crashed, websites for major political parties were hijacked, and a counterfeit letter appeared from the prime minister apologizing for removing the statue. Then, hackers began overloading routers and switches across the country. Two major banks had to shut down operations, losing millions, and half of the nation’s news outlets were knocked out. Most servers had to be disconnected, and the rest were so busy trying to protect themselves that Estonia’s Internet in essence stopped functioning.
After more than a week of crippling cyberattacks, the assault subsided and Estonian online security officials along with foreign experts were able to restore service. They also traced some of the machines used in the attack back to Russian government offices. Moscow denied involvement, and the government machines themselves could have been compromised and controlled by hackers elsewhere, but the lesson remains: Do not underestimate the real-world power of hackers in large numbers.
Target equals: America’s Achilles Heel
The Pentagon doesn’t. Every day, its electronic defenses take hits from hundreds of cyberattacks, some of which have been successful. Since 2006, the virulence and volume of attacks have surged dramatically. Electronic attacks on the Department of Homeland Security have tripled over the last two years, and those on military networks have increased 55 percent. One former high-ranking national security official called it “espionage on a massive scale.” In June 2007, an assault forced the Department of Defense to take as many as 1,500 computers offline, downing the Pentagon’s unclassified e-mail system. In other cases, top-flight military units have been hacked, and the Pentagon’s network vulnerabilities, detailed maps of Department of Defense facilities, and U.S. military war plans have been posted on the Web for the world to see. In 2007, a breach at the State Department put cia agents around the world at risk.
Perhaps the most worrying trend is that numerous attacks appear to be coming from foreign nations that are enemies of the United States, particularly China and Russia, as well as locations in Europe. In early June, congressmen reported that hackers in China have cracked multiple computers and accessed sensitive information inside the offices of American lawmakers, right on Capitol Hill. This has been going on since 2006. BusinessWeek reported that from 1998 to 1999, hackers stole large amounts of unclassified information from the Defense Department, nasa, the Energy Department and numerous weapons labs (April 10). The destination for some of the data was inside Russia. In 2004, hackers thought to be in China stole classified data from defense contractor Lockheed Martin, Sandia National Labs and nasa. Last year, China struck again, as reported by BusinessWeek: “2007. A new form of attack, using sophisticated technology, deluges outfits from the State Dept. to Boeing. Military cyber security specialists find the ‘resources of a nation-state behind it’ and call the type of attack an ‘advanced persistent threat.’ The breaches are detailed in a classified document known as an Intelligence Community Assessment. The source of many of the attacks, allege U.S. officials, is China. China denies the charge” (ibid.).
The U.S. administration recognizes the gravity of the cyberthreat and is spending tens of billions of dollars to defend against it. But those who are trying to protect the nation’s security online face a mountainous task. There are a multitude of government and military agencies trying to fight cyberwarfare that must coordinate with each other as well as with the private sector, all the while tiptoeing through a maze of legal and bureaucratic red tape that restricts military and cyber security enforcement, but which hackers don’t think twice about. In comprehensive cyberattack simulations such as Cyber Storm i and ii—in which the private sector disclosed attacks quickly and yielded to a higher authority, unlikely advantages in a real-world situation—the results are typically failures.
Then there’s the sheer volume of information the U.S. has to protect. The Pentagon alone uses millions of computers on tens of thousands of networks at hundreds of sites in dozens of countries. In addition to this, U.S. defenses are tied to hundreds of private sector defense contractors. Beyond the defense establishment, hackers can and have also targeted other essential national infrastructure: electrical grids, banks, transportation systems, news networks, government agencies and important businesses.
These contractors have weapons systems and other critical secret data stored on their networks that must also be secured. Inevitably, some systems are older and more vulnerable to sophisticated new viruses, while others are improperly administered. Even up-to-date systems totally miss cleverly disguised viruses, allowing attackers to track keystrokes, take screen shots and suck out loads of information. Hackers say there’s always at least one machine unprotected. And it only takes one.
Add all this to the fact that cyberwarfare favors the attacker. The defender must always react to the assailant, who chooses the time, place and method of the attack, which is always cloaked with anonymity, could inflict virtually unlimited damage, and can be waged by as few as one person located anywhere in the world at any time. All for less than the price of one m-16.
For the sprawling, mighty United States and its military, it is a starkly naked Achilles heel. This is the one thing that could easily and rapidly bring the nation to a standstill.
The more well-connected and technologically capable we get, the more vulnerable we are.
And the West is constantly getting better-connected.
In doing so, the military necessarily must tie its systems to civilian systems, where infections are even easier to start and spread. Budget-minded planners have also opted for off-the-shelf network security products and even security software developed in foreign nations. The U.S. Army’s advanced Future Combat Systems project makes soldiers even more dependent on the network.
Answer equals: USBIP
If independent, oftentimes teenage attackers motivated by ideologies as simple as voyeurism and resentment for authority have caused and can cause so much trouble, what happens when unified, ideologically motivated terrorists and enemies with the resources of a nation-state really begin pouring it on? Estonia would be merely a trial run.
A targeted and sustained assault on just a few of the nation’s key infrastructures—some of our already-faltering financial institutions, for example—could disrupt our economy, explode investor confidence and kill the dollar. Cyberassaults on oil and energy information systems could spike fuel prices. Attacks on transportation infrastructure could delay, diffuse and disrupt the nation’s economic bloodstream. Resultant fuel, food and energy shortages could spark widespread crises and even riots that would cost billions of dollars and possibly hundreds or thousands of lives.
But outright attacks on our military’s networks, especially coupled with infrastructure damage and resulting civil upheaval, could be nationally deadly. The most advanced military in the world relies on the most complex information systems to sustain an unprecedented and ultra-complex organization of logistics. Should those systems malfunction before or during a time of national crisis, ammunition could arrive late, units could be assigned incorrectly, helicopters might never deploy—and, worst-case scenario, some of our own weapons could conceivably be retargeted.
Trumpet editor in chief Gerald Flurry has monitored this vulnerability since January 1995: “America is the greatest superpower this world has ever known. But we have a very vulnerable point in our military—our own Achilles heel. … Exploiting this vulnerable point may trigger the greatest shock in the history of warfare! … Computer dependence is the Western world’s Achilles heel, and within a few years this weakness could be tested to the full.”
As the basis of his analysis, Mr. Flurry pointed to a key Bible prophecy that might be fulfilled in part by cyberwarfare: “Moreover the word of the Lord came unto me, saying, also, thou son of man, thus saith the Lord God unto the land of Israel; An end, the end is come upon the four corners of the land. … They have blown the trumpet, even to make all ready; but none goeth to the battle: for my wrath is upon all the multitude thereof” (Ezekiel 7:1-2, 14).
Even though the modern nations of Israel, including the U.S., Britain and the Jewish nation, sound an alarm of impending attack and expect their mighty armed forces to respond, “none goes to battle.” There are a variety of ways the immediate future could play out, but one thing is certain to happen: Ezekiel 7.
God has revealed these future events—as well as ultimately good news for our nations. To learn more about America’s vulnerabilities and its immediate future, request, download or read online at
theTrumpet.com Herbert W. Armstrong’s book that contains the answers to these problems as well as the awe-inspiring hope for our future: The United States and Britain in Prophecy.